DD-Androideasy and smali
DD-Android Easy
链接:https://github.com/ThunderJie/CTF-Practice/tree/master/CTF-Andorid%20Reverse/DD%20-%20Android%20Easy
解题思路:
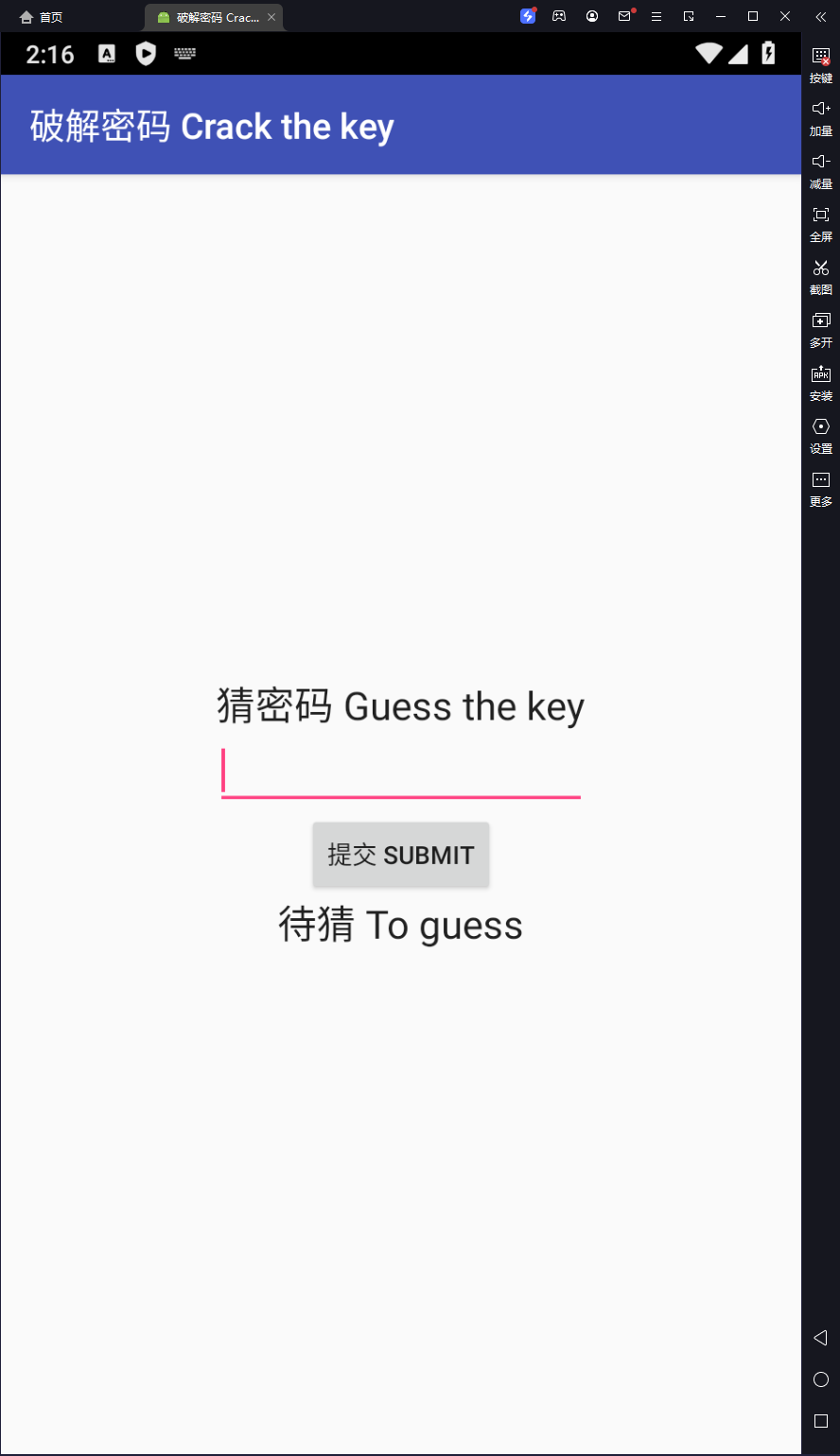
下载完成后发现是.zip格式,将后缀改为.apk格式,安装到模拟器中,发现是输入注册码的题目
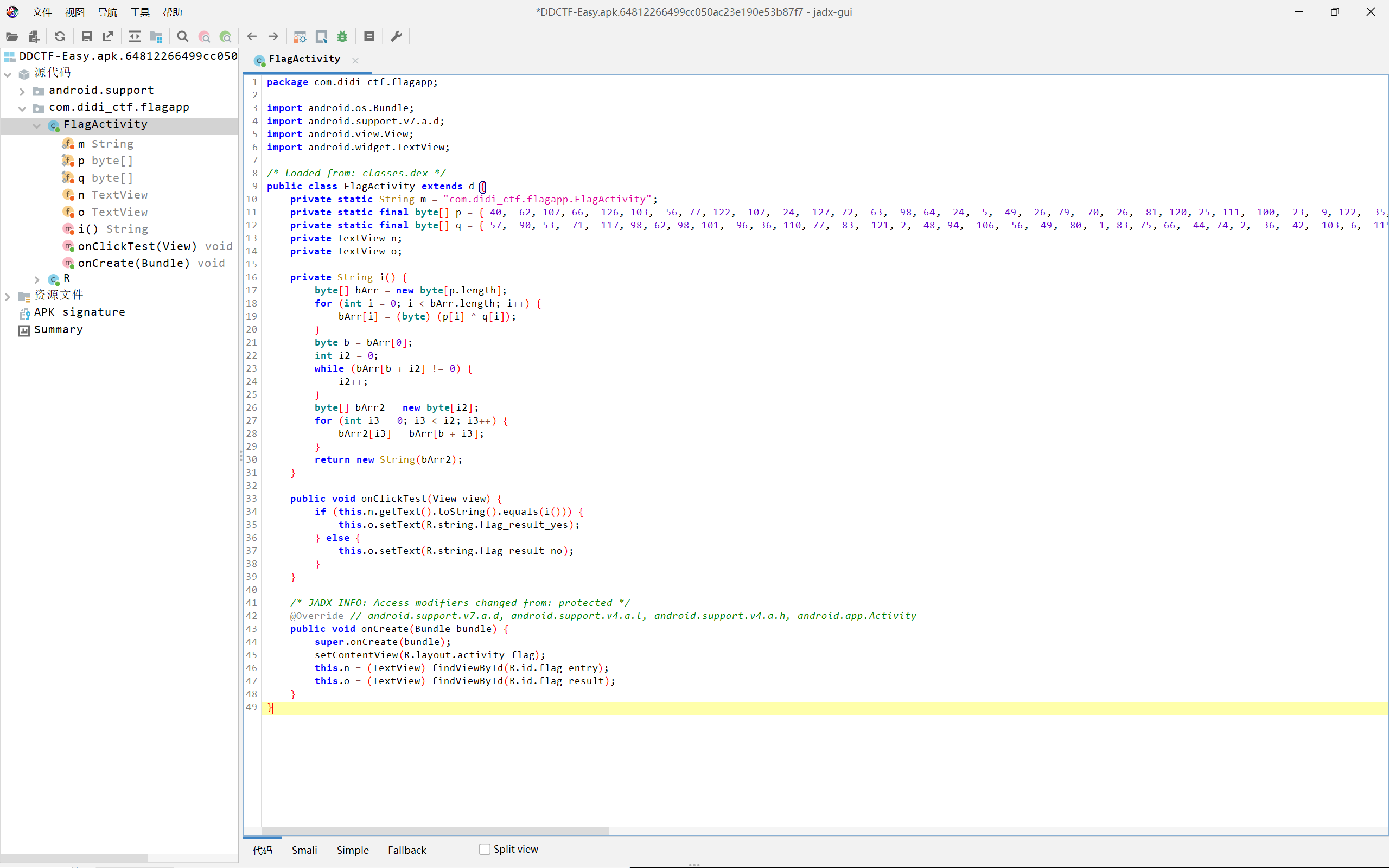
用jeb打开分析
可以看出只要得到字符串i的值便可以得到flag
解密脚本:
p = [-40, -62, 107, 66, -126, 103, -56, 77, 122, -107, -24, -127, 72, -63, -98, 64, -24, -5, -49, -26, 79, -70, -26, -81, 120, 25, 111, -100, -23, -9, 122, -35, 66, -50, -116, 3, -72, 102, -45, -85, 0, 126, -34, 62, 83, -34, 48, -111, 61, -9, -51, 114, 20, 81, -126, -18, 27, -115, -76, -116, -48, -118, -10, -102, -106, 113, -104, 98, -109, 74, 48, 47, -100, -88, 121, 22, -63, -32, -20, -41, -27, -20, -118, 100, -76, 70, -49, -39, -27, -106, -13, -108, 115, -87, -1, -22, -53, 21, -100, 124, -95, -40, 62, -69, 29, 56, -53, 85, -48, 25, 37, -78, 11, -110, -24, -120, -82, 6, -94, -101] |
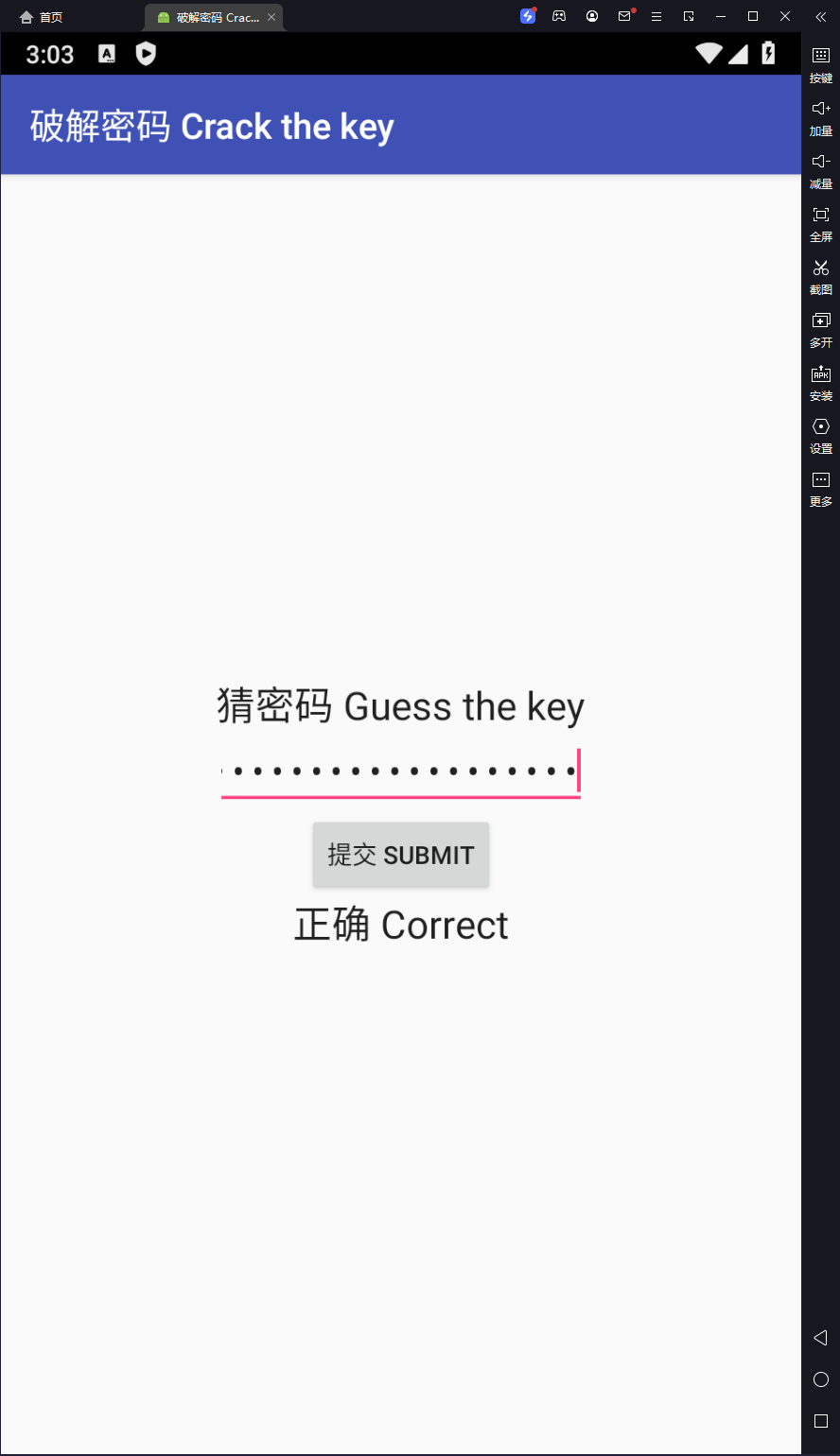
运行得到 flagDDCTF-3ad60811d87c4a2dba0ef651b2d93476@didichuxing.com
smali
链接:
https://github.com/ThunderJie/CTF-Practice/tree/master/CTF-Andorid%20Reverse/smali
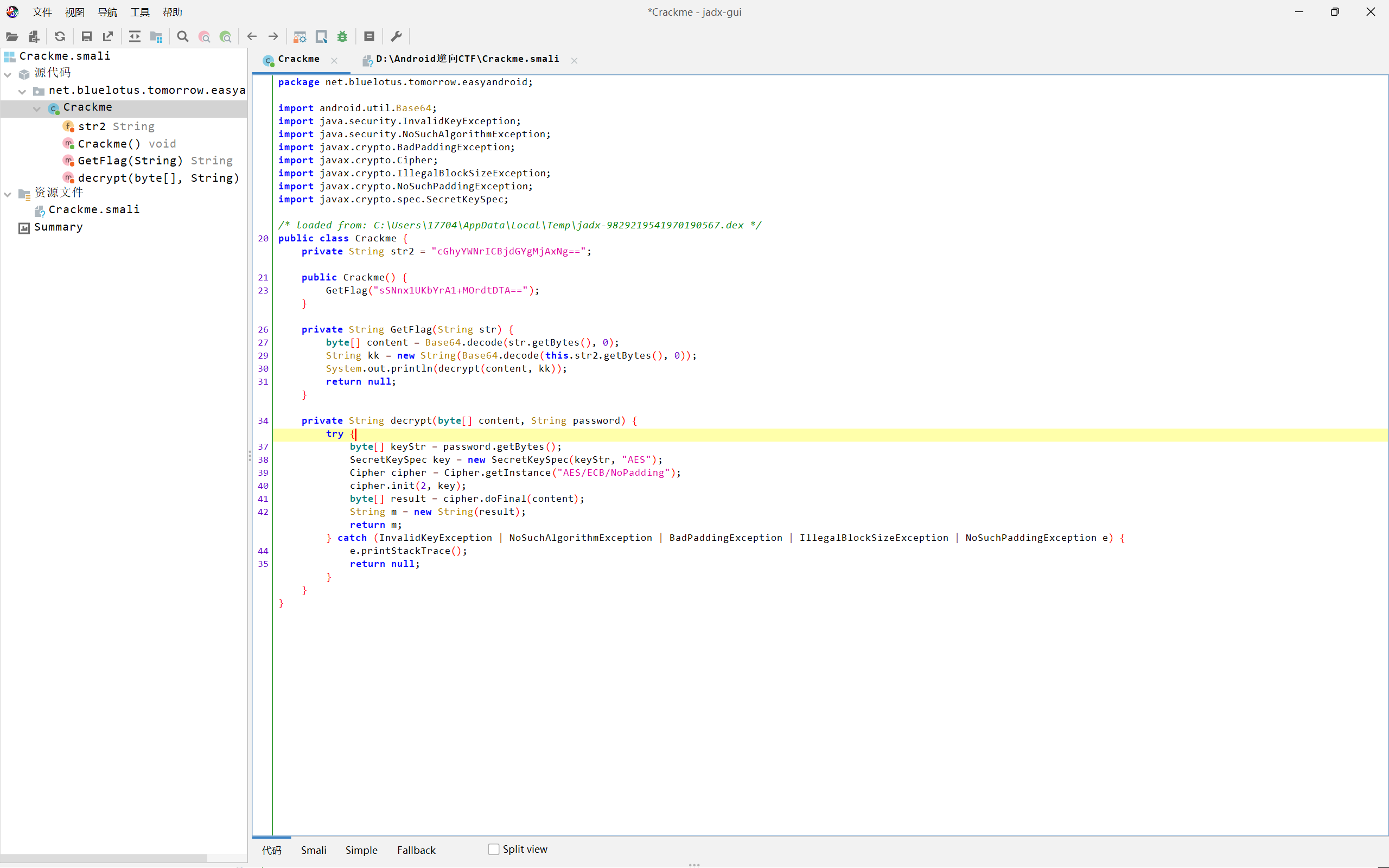
直接用jeb打开分析
分析看出是2次base64,一次AES,直接使用python编写脚本
解密脚本:
import base64 |
运行得到flag:b’PCTF{Sm4liRiver}’
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来自 Hexo!